Elora Engine Architecture Context
Structured feature and architecture context for what Elora can do today, including master pipeline execution and runtime evidence capture.
Structured feature and architecture context for what Elora can do today, including master pipeline execution and runtime evidence capture.
Start with Snapshot, then use the left navigation for deeper context pages (pipeline, runtime evidence, and governance replay).
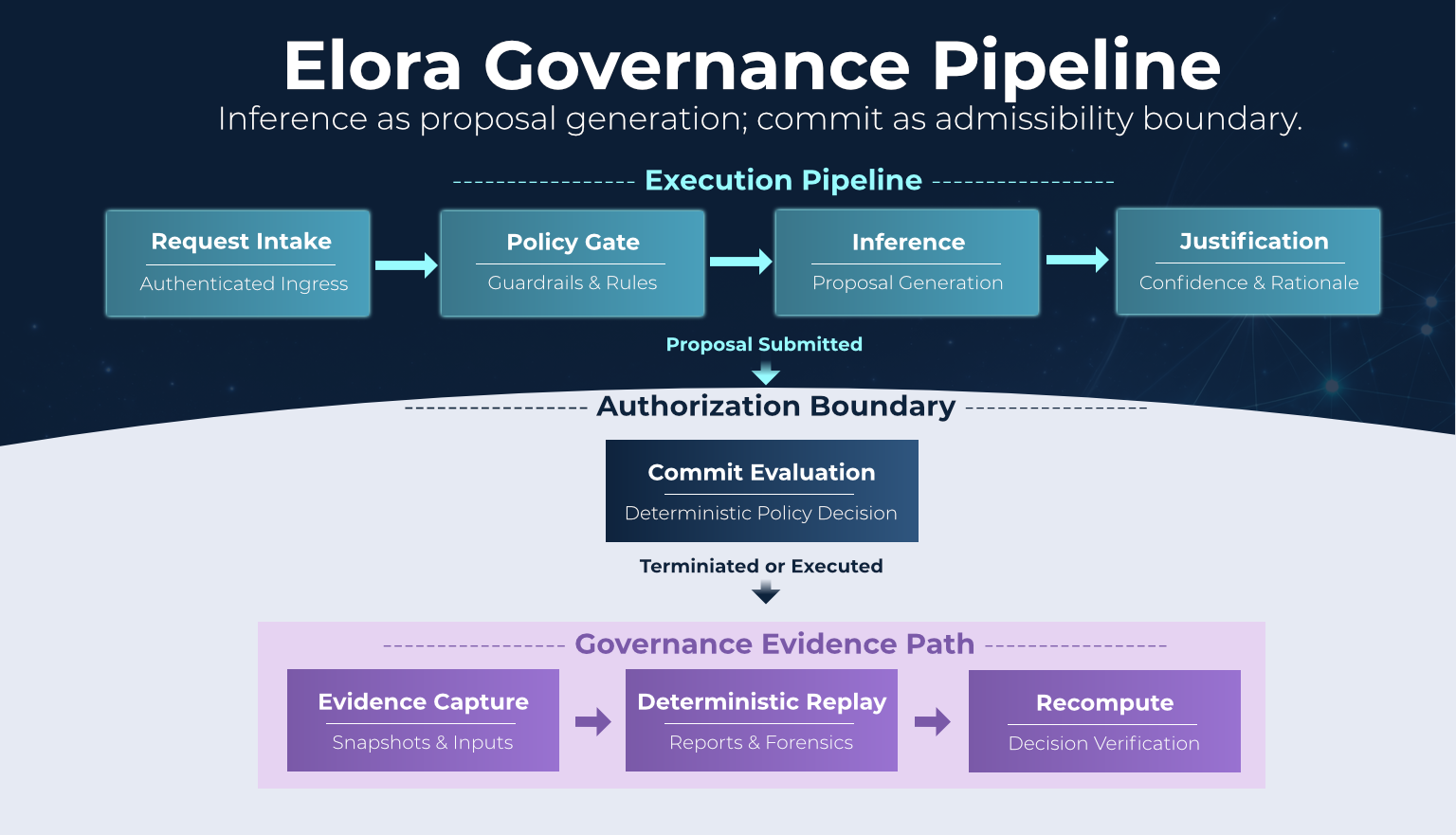
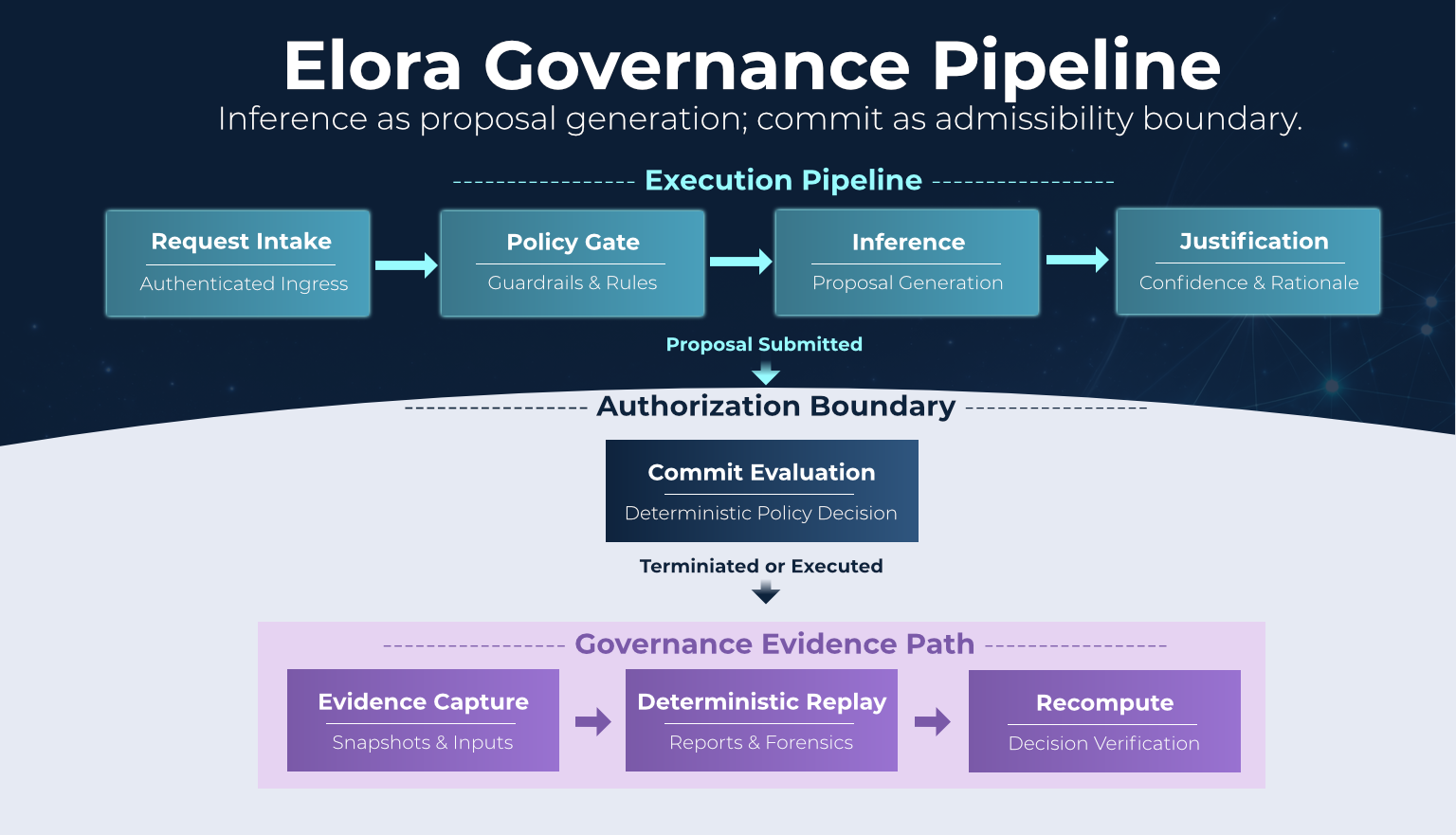
Elora can also be understood as a layered governance architecture that separates proposal generation from execution authority.
The layered model explains how requests move from trusted ingress through proposal generation and admissibility evaluation before any execution occurs.
The Elora project does not claim invention of cryptographic governance primitives. It applies established distributed-systems security mechanisms to AI runtime governance in a structured control-plane architecture.
AI governance is often discussed as if it requires entirely new cryptographic frameworks. In practice, the required primitives already exist and have secured distributed systems for decades. Elora applies these mechanisms so governance decisions can be reproduced and verified rather than asserted procedurally.
Caddy is used as the HTTPS edge gateway and routing boundary for engine surfaces. Runtime request authorization is enforced in the engine using bearer API key checks plus signed request validation with timestamp-skew controls.
Some public-safe status surfaces are intentionally exposed by design; protected runtime and admin surfaces require authenticated access. For async runtime flows, the engine issues short-lived job IDs and job tokens after authorized start requests so status polling remains scoped.
Before inference, Elora captures runtime evidence for prompt, memory, and knowledge stages. These are first-class pipeline events and not passive metadata.
Prompt data is captured as encrypted-at-rest evidence with deterministic hash linkage; memory and knowledge resolution are captured with snapshot references to support deterministic commit evaluation and replay.
Elora uses proven infrastructure primitives such as SHA-256 hashing, HMAC signatures, hash-linked replay integrity fields, and TLS-backed transport trust for verifiable evidence paths.
The architecture separates reasoning from execution so the control plane can evaluate admissibility at commit before actions occur.
Inference produces proposals; commit authorizes or blocks outcomes using captured policy, authority, prompt-hash, memory, and knowledge context.
Elora discloses architecture, governance models, and operator design patterns while protecting sensitive runtime contracts and deployment internals.
This keeps safety primitives inspectable and portable without exposing operational attack surface details.